It allows security professionals to intercept and inspect HTTPS communications on target devices after installing the appropriate SSL/TLS certificate. It is designed for offensive security testing and research scenarios, where manipulating requests and responses provides deeper insights into system resilience.
⚡ In short, the FlowTamper Proxy gives testers and researchers fine-grained control over live traffic, making it invaluable for exploit development, vulnerability validation, and protocol security research.
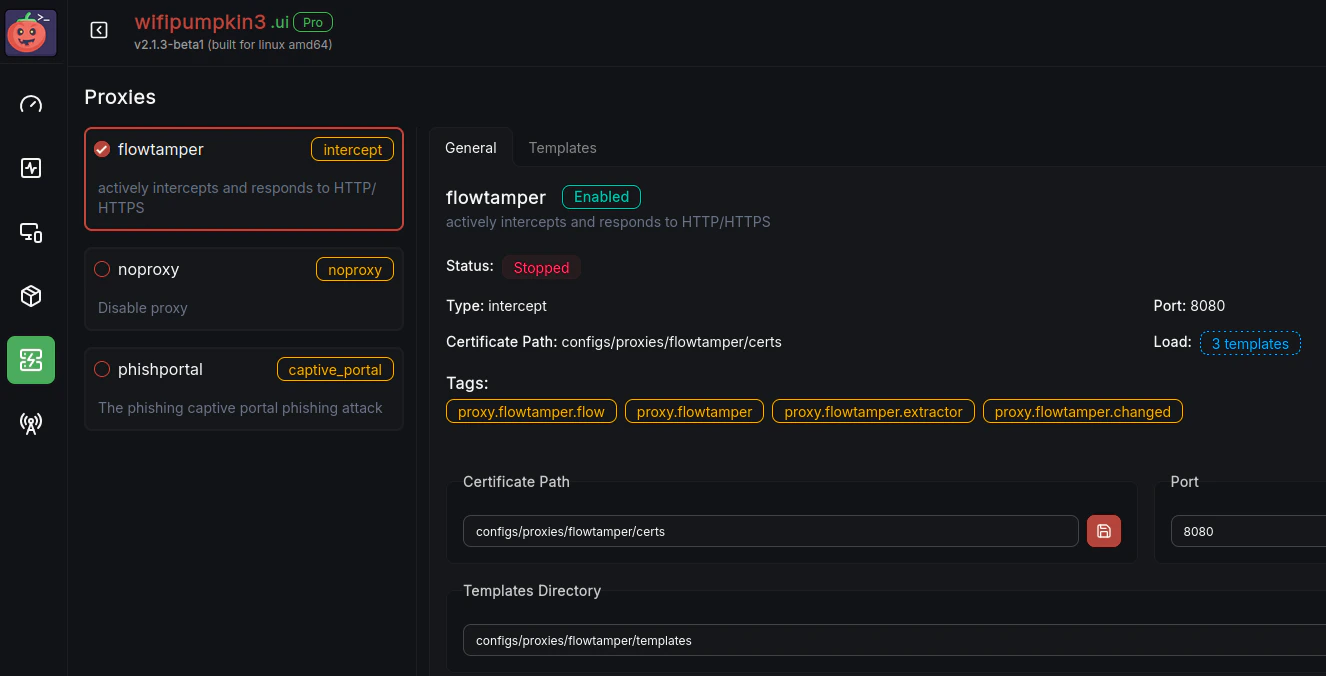
Flowtamper
Flowtamper Web UI Interface
.yaml templates to filter, extract, or modify network traffic in real-time, making it a powerful tool for red team operations, security research, and testing.
Overview
🔑 Key Capabilities
- Intercept & Modify Traffic: Change HTTP/HTTPS headers, cookies, parameters, and body content on the fly.
- Session & Auth Testing: Inject, strip, or alter authentication tokens (JWT, Bearer, cookies) to assess session management flaws.
- Bypass & Exploitation: Test WAF/IDS evasion, exploit injection points (SQLi, XSS), and simulate edge-case client behaviors.
- Sensitive Data Extraction: Detect leaked API keys, tokens, or secrets by tampering with API calls.
- Protocol Research: Study how servers, APIs, or IoT devices react to malformed or unexpected traffic.
🎯 Use Cases
- Penetration Testing: Validate vulnerabilities like IDOR, weak authentication, or improper input validation.
- Web & API Security: Analyze and exploit insecure headers, caching issues, and API flaws.
- Mobile & IoT Research: Intercept app/device traffic to discover hidden APIs or weak protocol implementations.
- Academic & Lab Research: Experiment with protocol robustness, WAF bypass techniques, and new attack vectors.